Chainlink stands at the forefront of enhancing security and compliance within smart contract-enabled blockchain networks. By enabling direct access to real-world data, Chainlink ensures that blockchain applications can operate with the same level of trust and verification as traditional systems. This integration is crucial for a wide range of applications, from financial services requiring Know Your Customer (KYC) and Anti-Money Laundering (AML) compliance to any form of digital agreement that needs to securely verify the identity of parties involved.
What is Chainlink?

Overview
Chainlink is a decentralized oracle network that plays a critical role in bridging the gap between smart contracts on blockchain networks and real-world data. It enables smart contracts to securely interact with external data.
Key Features of Chainlink
- Decentralized Data Oracles. Chainlink's network of decentralized oracles ensures that data fed into smart contracts is accurate and tamper-proof, mitigating risks associated with relying on a single data source.
- Smart Contract Connectivity to Real-World Data. It facilitates the seamless integration of external data sources, such as financial market data, weather information, and much more, enabling smart contracts to execute based on inputs from the real world.
- Chainlink VRF (Verifiable Random Function). This feature provides a secure and provably fair source of randomness for blockchain applications, crucial for gaming, NFTs, and any application requiring random number generation.
READ: "What is Chainlink"
The Role of Chainlink in Authorization and Identity Verification
When it comes to authorization and identity verification, Chainlink's role becomes even more crucial. By connecting smart contracts with external data sources, such as governmental identity databases or digital identity verification services, Chainlink enables the creation of blockchain applications that require verified human identities. This capability is essential for applications that must adhere to regulatory standards or for those seeking to mitigate the risk of fraud.
Moreover, Chainlink's decentralized nature ensures that the process of identity verification is not only secure but also resistant to manipulation. By leveraging multiple independent oracles to fetch and validate data before it's provided to a smart contract, Chainlink ensures a level of reliability and trustworthiness that centralized data sources cannot match. This decentralized approach to authorization and identity verification opens up new possibilities for blockchain applications, making them more accessible, compliant, and secure for users around the globe.
Key Use Cases of Chainlink in Authorization and Identity
The integration of Chainlink's decentralized oracle network into the domain of authorization and identity verification heralds a new era of security, efficiency, and compliance for blockchain applications. By leveraging real-world data and external verification services, Chainlink enables smart contracts to perform functions that were previously unthinkable in the blockchain space. Here, we explore several key use cases where Chainlink's technology significantly impacts authorization and identity verification processes.
E-Signatures
In the digital age, e-signatures have become the norm for legally binding agreements, eliminating the need for physical presence or paper-based documents. Chainlink oracles facilitate the integration of blockchain applications with leading e-signature providers like DocuSign. This integration ensures that e-signatures can be verified and recorded on the blockchain, providing immutable evidence of agreement and authorization. Furthermore, by enabling smart contracts to interact with e-signature solutions, Chainlink opens the door to automated contract execution based on the completion of digitally signed agreements, thereby streamlining business processes and reducing the time and cost associated with manual verification.
Biometrics for Smart Contract Authorization
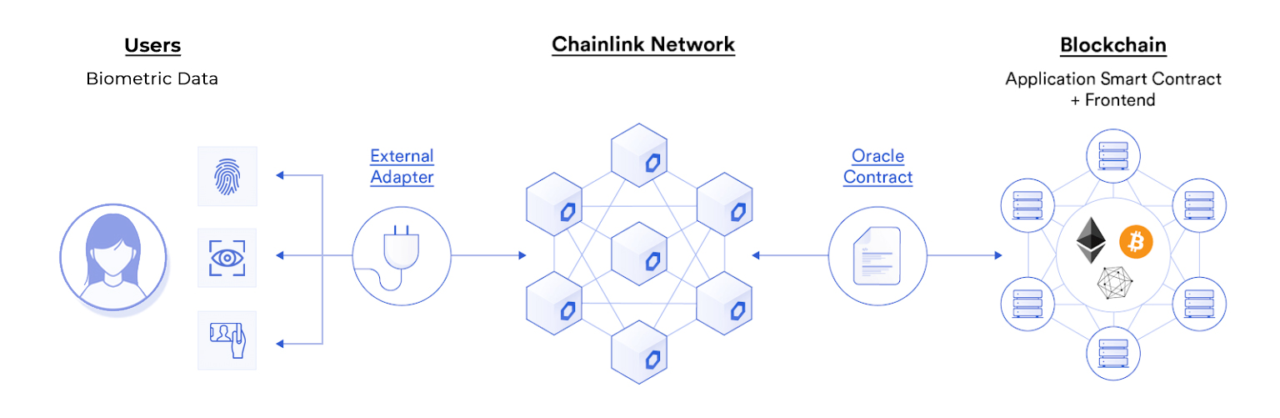
Biometric verification offers a high level of security and convenience for identity verification. It leverages unique physical characteristics such as fingerprints or retinal patterns. This use case is particularly relevant for access control systems and secure transactions. It also helps with identity verification processes that require a high degree of trust and security. By connecting smart contracts with biometric databases, blockchain applications can achieve a new level of security and fraud prevention.
Credential Verification
Credential verification is crucial in numerous applications, from financial transactions requiring proof of funds to access systems demanding specific security clearances. Chainlink oracles play a pivotal role by securely relaying credential verifications from external systems to the blockchain. This capability allows smart contracts to automatically verify users' credentials in real-time, facilitating seamless transactions and interactions that require verified identity or authorization credentials. For example, a decentralized finance (DeFi) platform can use Chainlink to verify a user's creditworthiness or asset ownership before allowing them to participate in lending or borrowing services.
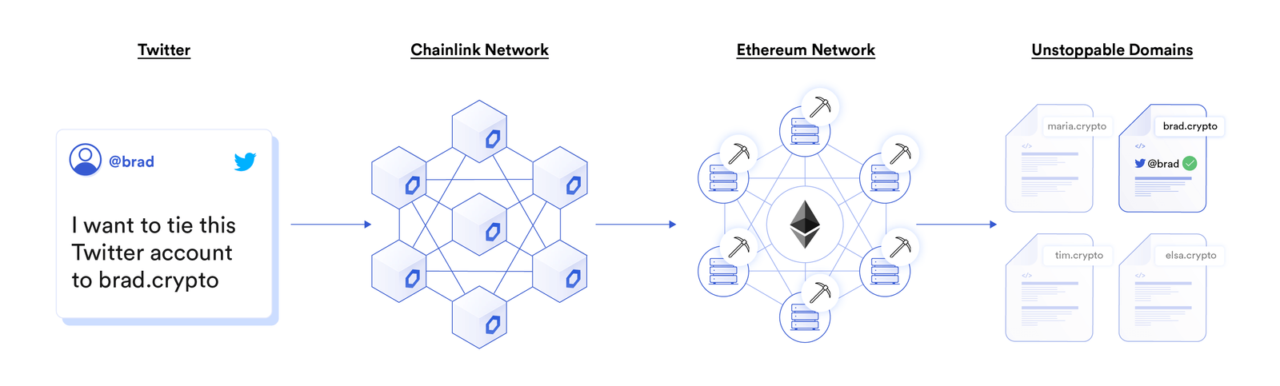
Social Media Identity and Domain Names
The integration of social media identities with blockchain applications enhances user experience by providing more intuitive and human-readable identifiers, such as domain names or social media handles. Chainlink oracles facilitate this by securely linking off-chain social media identities to on-chain addresses or domain names. This use case not only improves the usability of blockchain applications but also adds an extra layer of verification, as users can easily confirm the authenticity of the parties they are interacting with.
Intellectual Property Management
Chainlink's decentralized oracle network enables smart contracts to interact with external IP databases for verifying ownership. This application is particularly useful for copyright and trademark management, patent licensing, and royalty distribution. By automating IP verification and transactions through Chainlink, creators and owners can more efficiently manage their rights and receive payments, while users gain access to verified IP assets.
Contribution Bounties in Open Source Projects
Open-source projects can leverage oracles to automate the verification of contributions and the distribution of bounties. By connecting smart contracts with public code repositories like GitHub, Chainlink allows projects to automatically track contributions, verify the fulfillment of predefined conditions, and release payments to contributors. This application streamlines the contribution process, incentivizes open-source development, and ensures that contributors are fairly compensated for their work.
Conclusion
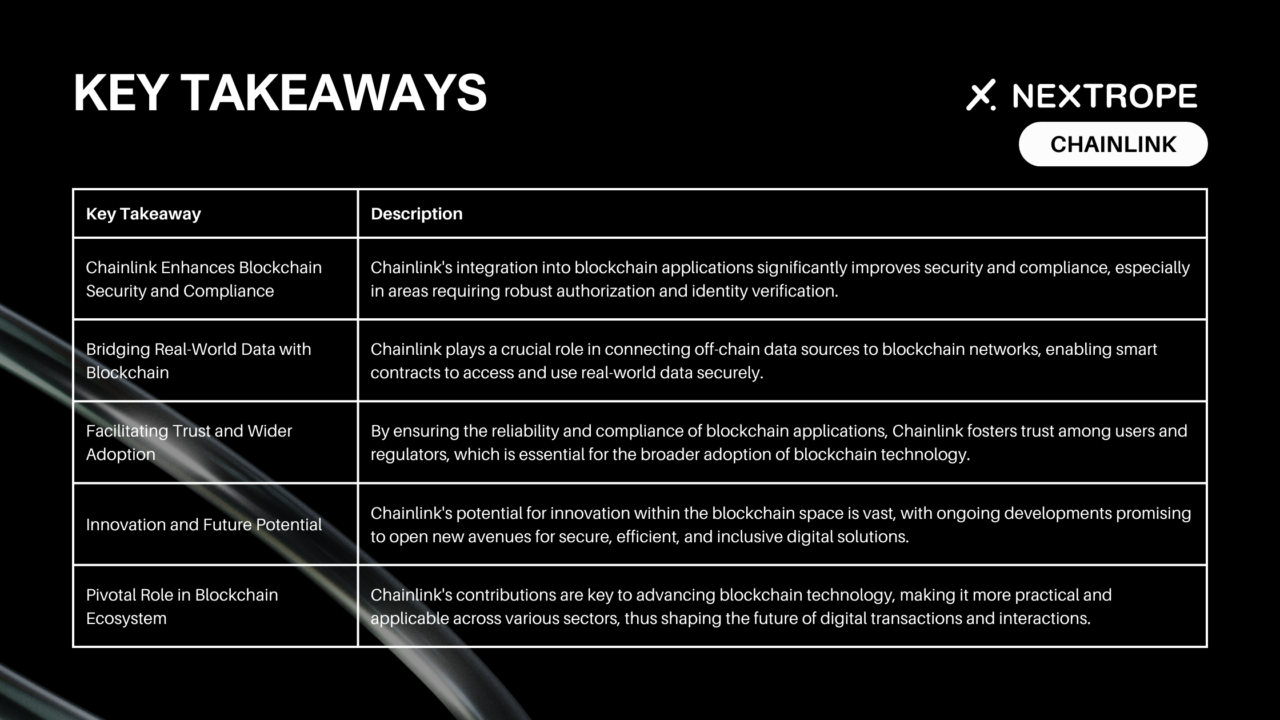
Chainlink significantly impacts blockchain, enhancing security and compliance, especially in authorization and identity. It bridges real-world data with blockchain, ensuring trust and wider adoption. As blockchain evolves, Chainlink's innovations promise a more inclusive digital future. Its key role in securing and streamlining blockchain applications marks a crucial step forward for digital interactions. Chainlink is pivotal for a secure, compliant, and efficient blockchain ecosystem, shaping the future of digital transactions.
If you are interested in utilizing Chainlink or other blockchain-based solutions for your project, please reach out to contact@nextrope.com
FAQ
Can Chainlink help with identity verification?
- Yes, Chainlink supports identity verification processes, such as e-signatures and biometric data checks, for blockchain applications.
How does Chainlink integrate with e-signatures?
- Chainlink can connect blockchain applications with external e-signature services, allowing for secure and verifiable signing processes.
Could Chainlink be used for anything other than security and identity?
- Chainlink's technology has potential applications beyond security and identity, such as in decentralized finance (DeFi) and supply chain management.
Does Chainlink protect user privacy during identity verification?
- Chainlink's use of decentralized oracles and secure data transmission suggests a focus on maintaining user privacy.
 en
en  pl
pl